During midterm week, students might need a little inspiration. And what’s more inspirational than a convicted felon exhibiting technological magic?
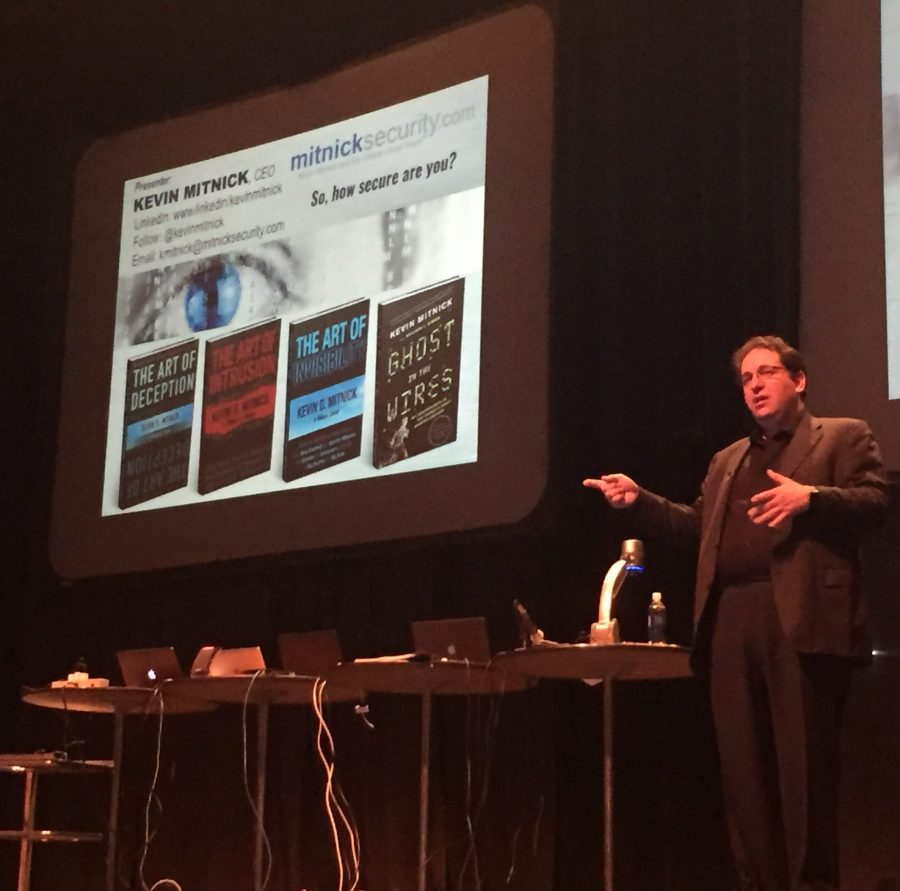
Not much, proved Kevin Mitnick as he delivered a demonstration-filled keynote address to end last week’s Business Symposium. He spoke Thursday at the Monroe Civic Center’s Jack Howard Theatre where admission was free to the public.
Mitnick, known by the U.S. Department of Justice as “the most wanted computer criminal in United States history,” is an American computer security consultant, author and hacker who is well-known for his highly publicized 1995 arrest after being on the FBI’s Most Wanted list.
During his black hat hacking days, Mitnick was pursued for hacking dozens of corporate systems, including IBM, Nokia, Motorola and Fujitsu.
After a total of five years in prison plus probation time, Mitnick now runs a consulting business as a white hat hacker, finding weaknesses in the security systems of companies that pay him to do so.
In an address that mainly emphasized the dangers of the “human factor” in breaching security, Mitnick demonstrated several different hacking techniques live to the large audience gathered Thursday night.
“Attacks these days don’t target the technology, necessarily, they target those who use the technology,” he said.
He said social engineering, which is the psychological manipulation of people to gain information, is what he largely depends on to hack.
Mitnick was once commissioned to physically break into an office to test the cyber strength of the company’s keycard system. He didn’t have to rely too heavily on computer hacking to get the job done. In fact, Mitnick gained access easily by making a copy of a keycard that an employee handed to him.
In another example, Mitnick gained access to Motorola’s MicroTAC source code just by making a few calls as he was walking home from work one day. When he asked for the source codes, a worker sent them to him using a security manager’s private access, although Mitnick was not at all cleared to receive the codes.
As Mitnick said, there are certain expectations for politeness that hackers can exploit to take advantage of ordinary people. This, paired with computer hacking abilities, can give someone access to almost any information they could want.
Mitnick further demonstrated that trusting unverified sources, whether they are people or Wi-Fi networks, can be dangerous when he took over a computer that connected to his wireless network.
He further wowed the crowd with the dangers of technology and the internet by hacking passwords, sending text messages from the cell phone numbers of others, and looking up social security and credit card numbers on the internet.
Connor Dixon, a senior computer science major, got the chance to meet Mitnick when he volunteered for a demonstration. For Dixon, Mitnick’s presentation proved that caution needs to be taken at all times.
“He showed us all the ways he can steal our information, or a company’s information, and all the tools he can use to do so,” Dixon said.
Dixon added that meeting Mitnick was one of the highlights of his time at ULM.